Link Key generation Encryption keys: The encryption key is generated... | Download Scientific Diagram
Link Key generation Encryption keys: The encryption key is generated... | Download Scientific Diagram

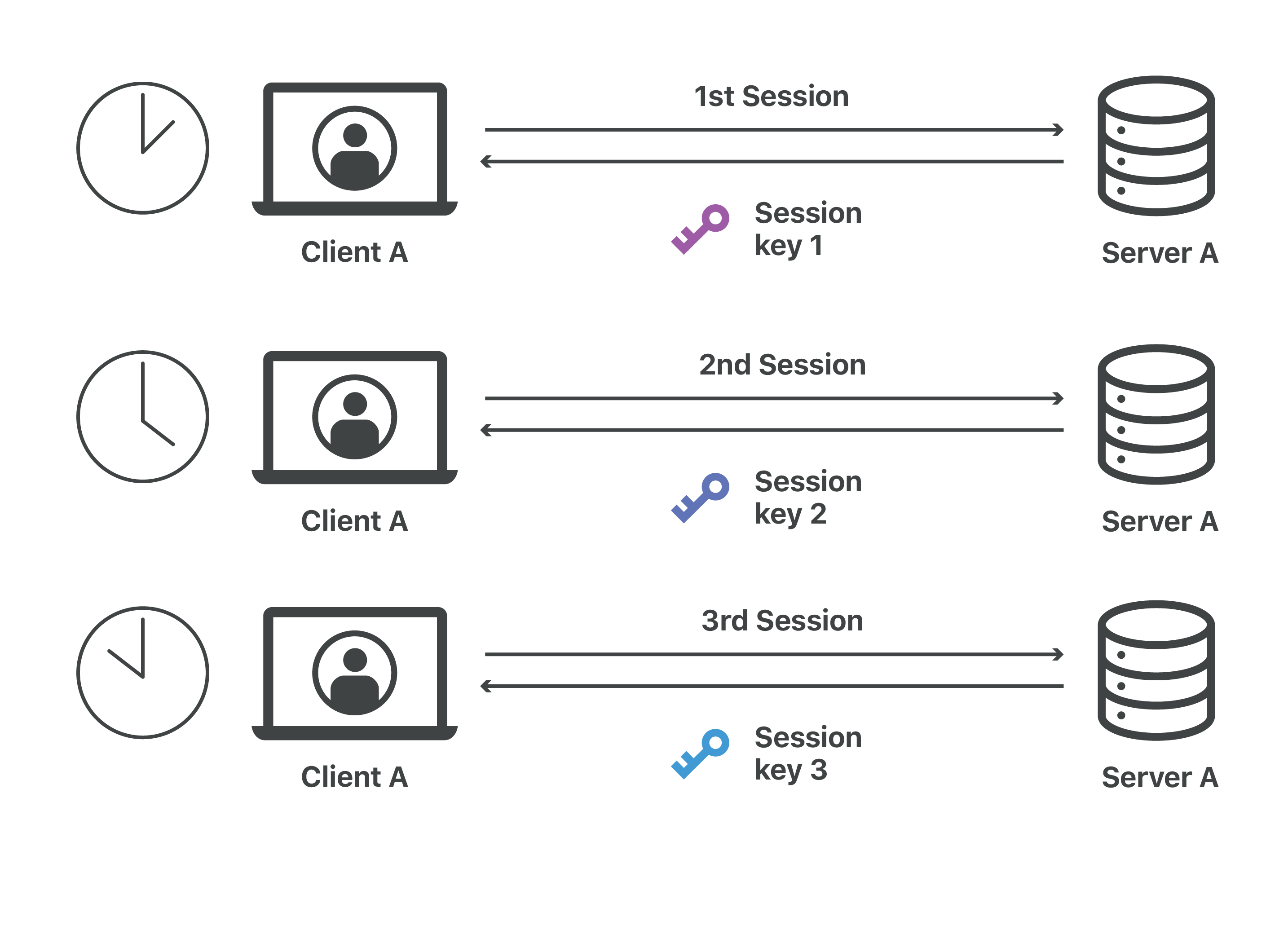
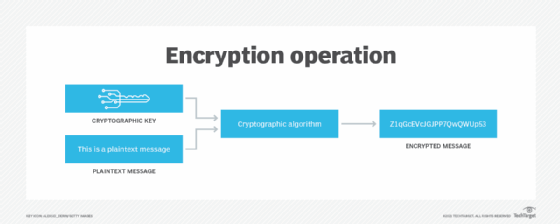
Demystifying KMS keys operations, bring your own key (BYOK), custom key store, and ciphertext portability | AWS Security Blog

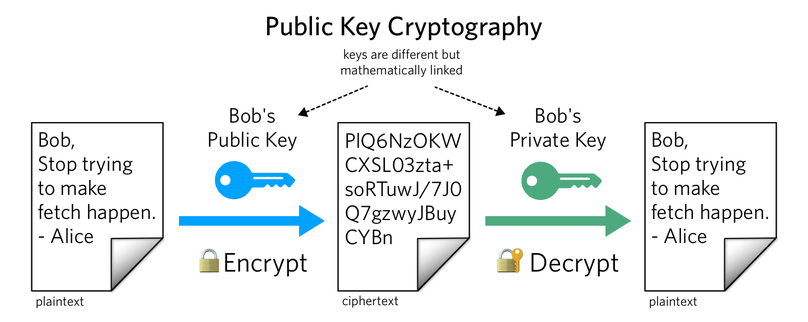
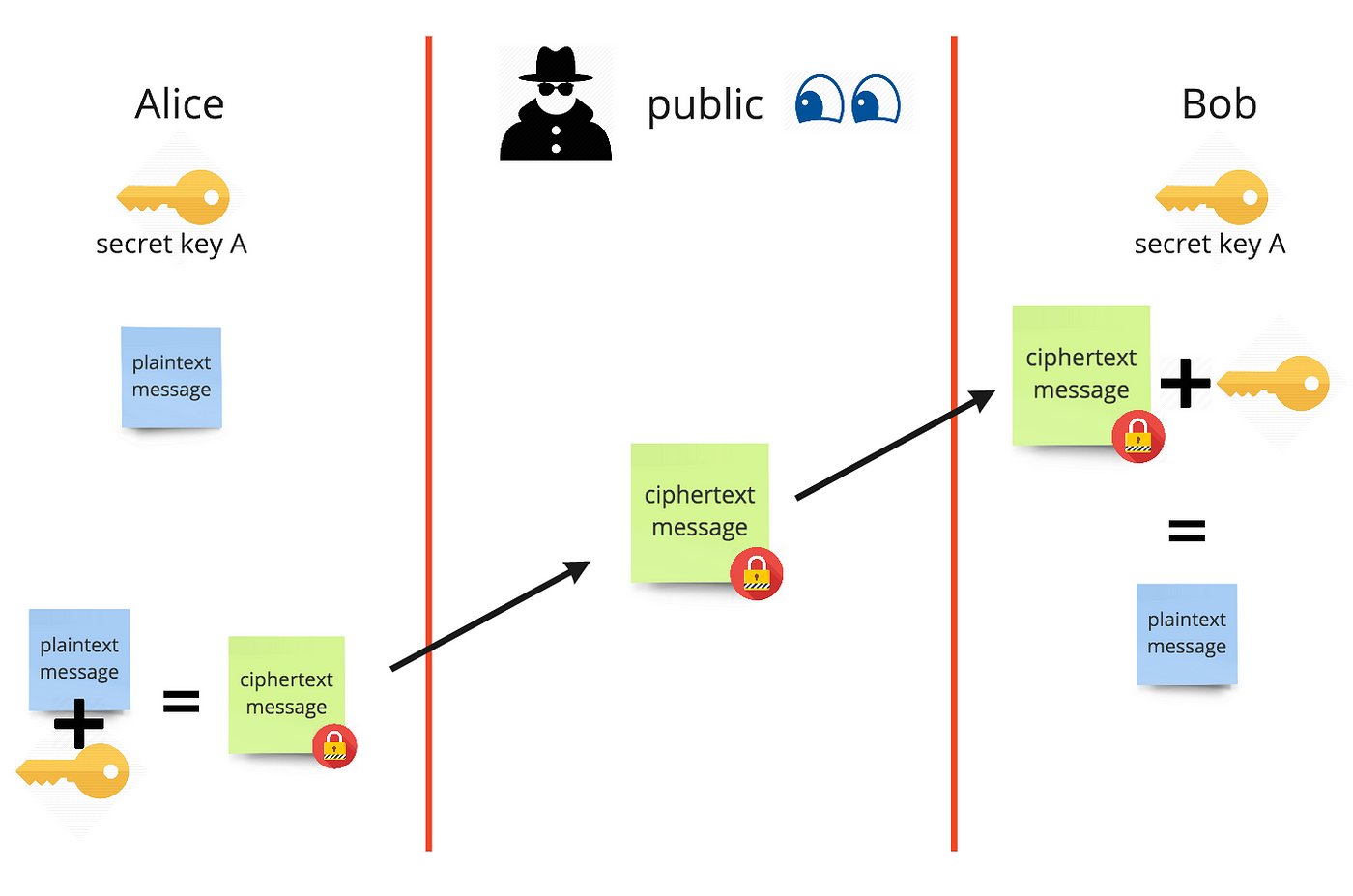
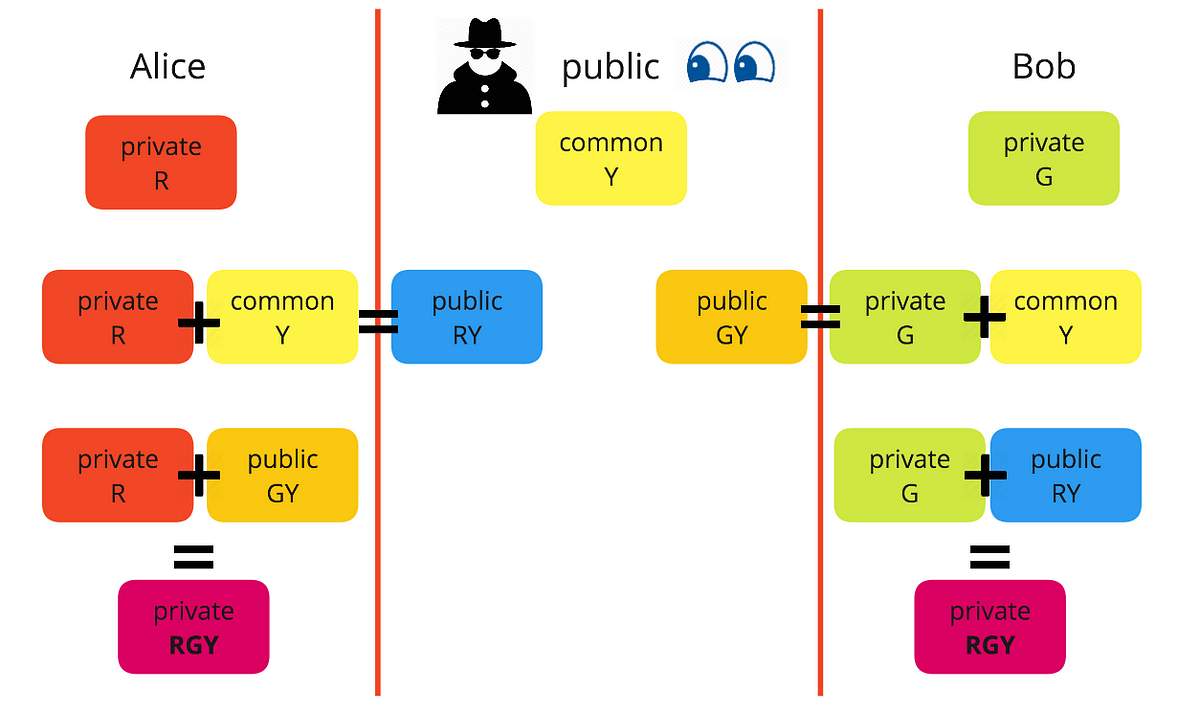
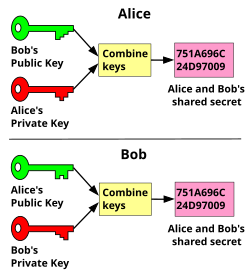
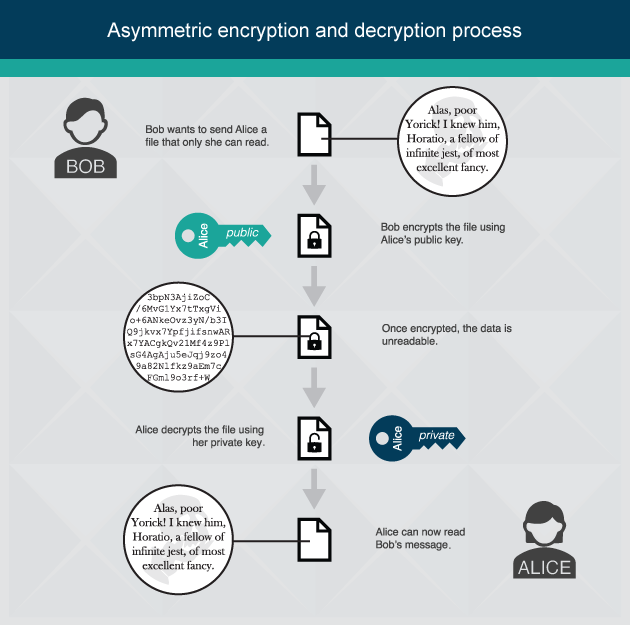
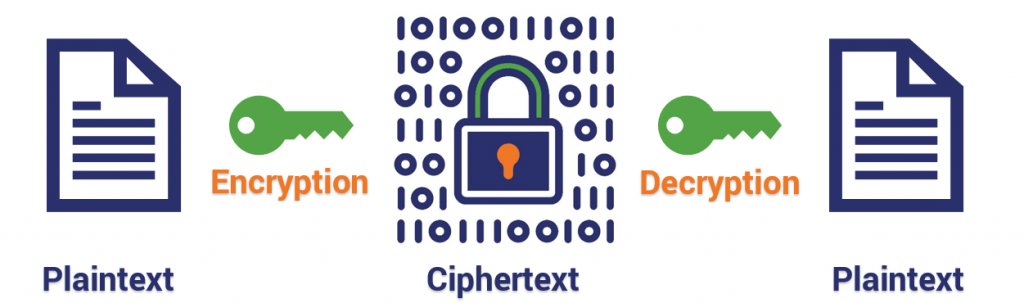
A Deep Dive on End-to-End Encryption: How Do Public Key Encryption Systems Work? | Surveillance Self-Defense
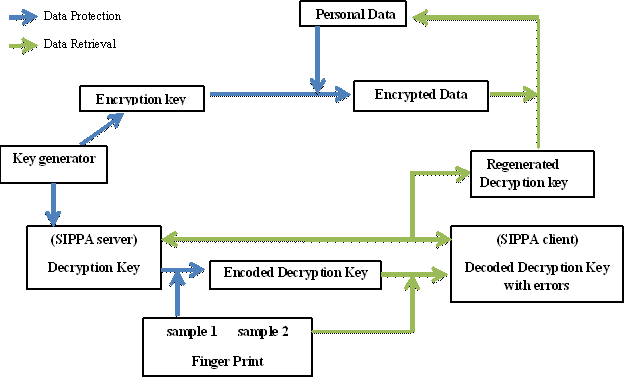
Generation of Cryptographic Keys from Personal Biometrics: An Illustration Based on Fingerprints | IntechOpen