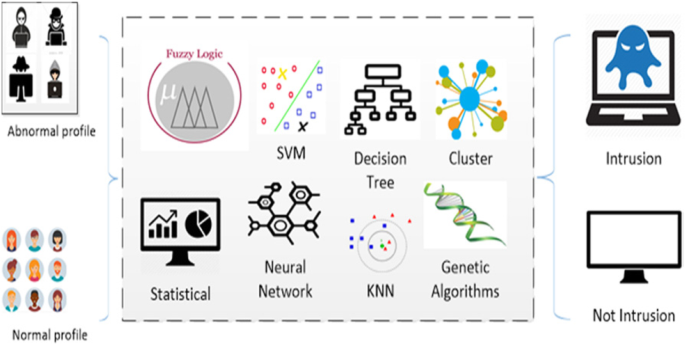
A survey on intrusion detection system: feature selection, model, performance measures, application perspective, challenges, and future research directions | SpringerLink

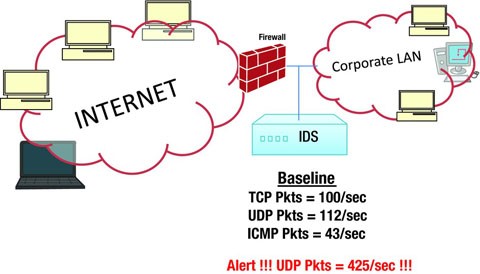
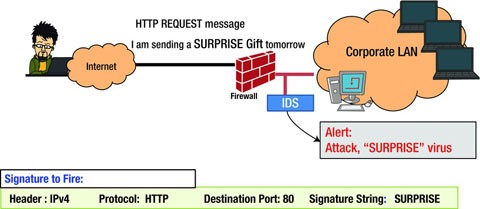
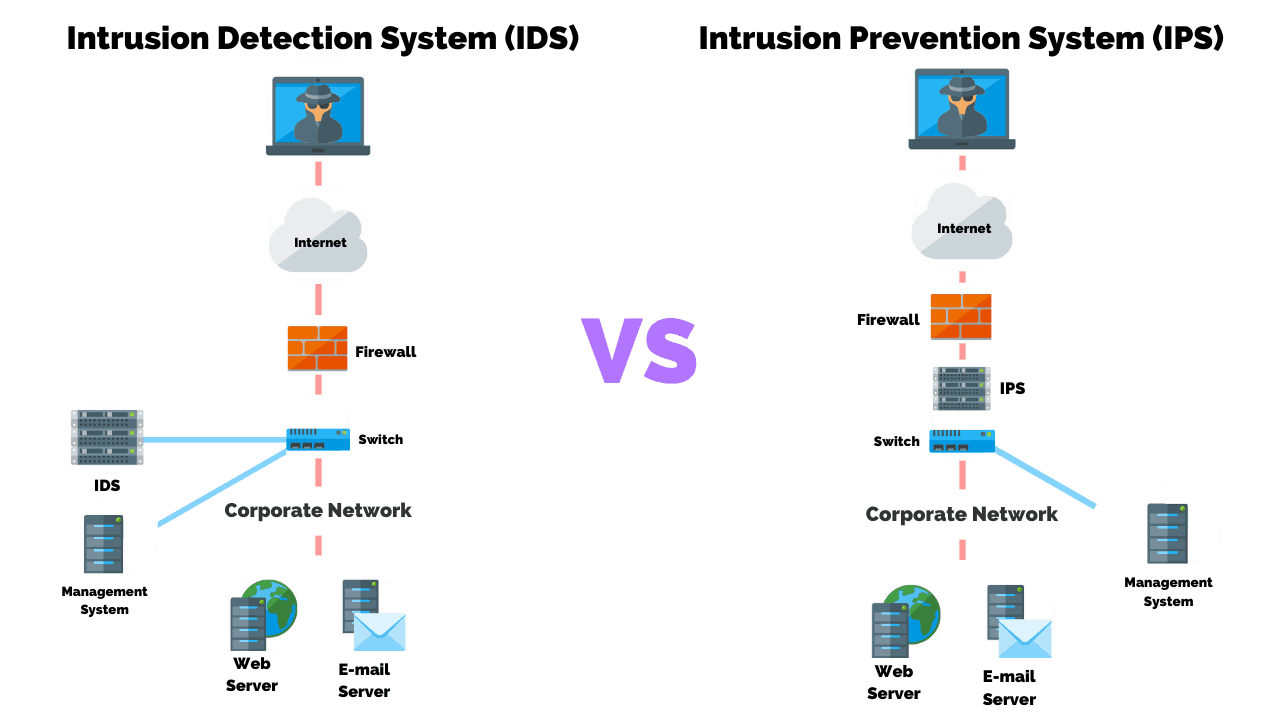
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security

Differential early diagnosis of benign versus malignant lung cancer using systematic pathway flux analysis of peripheral blood leukocytes | Scientific Reports

What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security




![Detections and alerts | Elastic Security Solution [8.5] | Elastic Detections and alerts | Elastic Security Solution [8.5] | Elastic](https://www.elastic.co/guide/en/security/current/images/alert-page.png)